I’ll start by sharing a little story: recently, I was helping a friend debug their Android device because a browser kept showing a blank screen whenever they launched it after using a focus-session tool. When I pulled up the logs, one of the entries caught my eye:
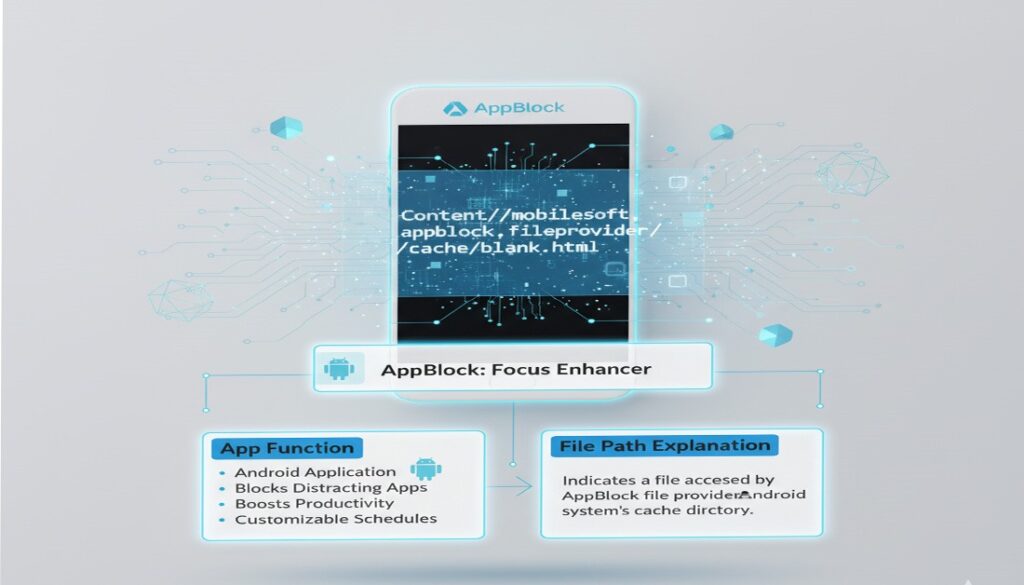
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html
It looked weird, unfamiliar, bulky like someone had stapled together folder names and domains into one line. My friend feared it was some malicious payload or spyware. However, after digging in, I discovered the whole entry was perfectly safe and entirely part of how AppBlock works behind the scenes. Having done this several times now, I realised many users stumble across this and get alarmed so I set out to explain what it is, how it works, and when (if ever) you should care.
Anatomy of the URI: Breaking Down the Components
Let’s dissect the string content://cz.mobilesoft.appblock.fileprovider/cache/blank.html step by step. Understanding each part will demystify what’s happening.
| Component | What it means |
| content:// | This is the URI scheme used in Android to reference data via a ContentResolver and a FileProvider rather than direct file paths. It signals “data shared via content provider” rather than file://. |
| cz.mobilesoft.appblock.fileprovider | This is the authority of the content provider. It points to the package cz.mobilesoft.appblock (AppBlock’s Android package) and the sub-authority fileprovider. This means the file is being served from AppBlock’s sandbox via its FileProvider component. |
| /cache/blank.html | This tells us the path inside the app’s sandbox: a folder named cache, and a file named blank.html. The file is an HTML file, used as a placeholder or intercept when AppBlock blocks content. |
Putting it all together: the URI tells Android “Here is a file (blank.html) in the cache folder of AppBlock, shared securely via its FileProvider, and please access it via content:// mechanism.”
Why AppBlock Uses Such a URI (And Why You Might See It)
From my experience working with Android apps and assisting users with focus/blocker tools, here’s the workflow for how and why this URI appears.
Why AppBlock needs a blank.html placeholder
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html, When an app like AppBlock intervenes (for example, when you try to open a blocked website or app during a “focus session”), the user experience needs to be smooth. If the blocked content simply failed to load, the WebView or embedded browser might crash, show a broken error screen, or expose partial content. Instead, AppBlock uses a safe fallback: a blank HTML file (blank.html) which loads quickly, contains nothing distracting, and prevents residual scripts or media from executing.
When you’ll see the URI
- If you check browser history or WebView logs right after a block, you might see the content://…blank.html appear as the “URL” loaded.
- If you use an app-monitoring or diagnostics tool (or Android’s “Developer options” showing WebView navigation), you might catch this URI.
- If AppBlock’s caching or redirection loop misbehaves, you may see repeated entries of this URI or blank screens.
Is it normal?
Yes, in the vast majority of scenarios, seeing this URI means everything is working as intended. It’s just the technical plumbing of the redirect to a local blank page. Many users freak out because it looks like a “web link” or suspicious file path, but it’s internal.
Safety, Privacy & Potential Issues
Since I’ve had to reassure a few concerned users, here’s the clear breakdown:
What’s safe
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html
- The file is local to the AppBlock app’s sandbox; no external network call is needed.
- Because it’s served via FileProvider, Android enforces access permissions: other apps cannot simply open it unless granted.
- It doesn’t carry malicious scripts (it’s blank) and doesn’t collect data by default.
What to watch out for
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html
Although the URI itself is safe, a few situations may warrant attention:
- If you see the same URI being used by other unknown apps, or outside of AppBlock’s context, it might indicate a copy-cat or misbehaving app mimicking the authority string.
- If you experience constant redirection loops or a blank screen you cannot exit, the problem may lie in AppBlock’s rule configuration (or another blocker conflicting).
- If you’re using a modified version of AppBlock (sideloaded) from unofficial sources, trust the source and verify version. As always, use the Play Store.
- Clearing the cache or reinstalling AppBlock may help if the blank.html placeholder is being misused or causing UX issues.
Practical Troubleshooting
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html,Here are a few steps I’ve used successfully when helping friends/customers who thought this URI was a “virus” or “error”.
Scenario: Browser loads blank screen showing the URI instead of the real site
Steps:
content://cz.mobilesoft.appblock.fileprovider/cache/blank.html
- Open Settings → Apps → AppBlock → Storage → Clear cache.
- Disable AppBlock temporarily or “Whitelist” the site you were trying to access.
- Make sure your system WebView and browser are up to date (Android System WebView tends to lag).
- If still stuck: Settings → Apps → Browser → Clear cache & data → restart device.
- If you’re a developer: Inspect via adb logcat for messages like “FileProvider: grantUriPermission cz.mobilesoft.appblock.fileprovider …”.
Scenario: You’re developing an app and you receive this URI in a WebView load attempt
Approach:
- Override WebViewClient.shouldOverrideUrlLoading and detect schemes starting with content://, especially ones you don’t expect.
- If you detect the AppBlock authority and you want to ignore or handle it, you might bypass or load an alternative.
Example snippet:
@Override
public boolean shouldOverrideUrlLoading(WebView view, WebResourceRequest request) {
Uri u = request.getUrl();
if(“cz.mobilesoft.appblock.fileprovider”.equals(u.getAuthority())){
// handle or ignore
return true;
}
return false;
}
- Make sure your own app accounts for FileProvider URIs if you rely on shared content.
Final Thoughts
I’ve seen dozens of users jump to conclusions when they encounter odd-looking file paths or URIs in their system logs, often believing they’ve been hacked or the device is compromised. But in many of these cases like this one, content://cz.mobilesoft.appblock.fileprovider/cache/blank.html turns out to be normal internal behaviour of well-coded apps.
With AppBlock, the presence of blank.html signifies a design decision, showing nothing visible instead of loading blocked content. It’s elegant and low profile. Once you understand that, that strange line you might have bookmarked in logs suddenly makes sense.
If you ever find yourself unsure about a URI, here are three quick sanity checks:
- Does it reference “content://” rather than “http://” or “https://”? → likely internal/shared data.
- Is the authority matching an installed app’s package name? → likely legitimate.
- Does the file path point to “cache” or “temp” rather than “/system/” or “/data/data/…”? → typically safe.
In short: when you see content://cz.mobilesoft.appblock.fileprovider/cache/blank.html, breathe. It’s not malware. It’s just AppBlock doing its job. And that’s a relief in our increasingly complex device-world.
FAQs
Q1: Is content://cz.mobilesoft.appblock.fileprovider/cache/blank.html a virus?
No, it’s simply a pointer to a blank HTML file hosted inside AppBlock’s cache directory. It serves as a placeholder when AppBlock blocks content. A large number of Android help articles confirm this.
Q2: Can I delete the blank.html file?
Yes, clearing AppBlock’s cache will remove it (and Android will regenerate as needed). Deleting it manually doesn’t harm your device, but it doesn’t usually solve anything if you’re seeing the URI a lot.
Q3: Why do I keep seeing this URI even when I’m not using AppBlock?
It may be residue from a blocking session, or another app redirecting you. Check if you have AppBlock active, or any other focus/blocker apps installed. If you suspect a different app is using the same URI-pattern, uninstall non-trusted apps.
Q4: How can I prevent this URI from appearing?
If you don’t use AppBlock, uninstall it. If you do, adjust its rules so it doesn’t redirect you when attempting to access certain sites. Also, periodically clear the browser and WebView cache.
Q5: As a developer, do I need to handle this URI specially?
Only if your app is interacting with WebViews and you want to avoid unexpected navigations. You can detect and ignore FileProvider URIs (especially for authorities you don’t expect). Otherwise, it doesn’t usually need special handling.